Two blog posts that give examples of what to expect are already available on Apple’s newly launched website for macOS and iOS security. One of the posts takes a close look at memory allocation in the XNU kernel, which is at the core of all Apple products, and the other discusses the improved security bounty process.
Without a doubt, the new website will grow into a vital tool for Apple security researchers, offering knowledge and acting as a center for submitting bounties. On the Apple Security Research website, you may also apply for an official Apple Security Research Device (SRD), which grants you exclusive access to iOS’s normally secured features and aids in the discovery of vulnerabilities.
As the core software libraries for macOS, iOS, iPadOS, watchOS, and tvOS are the same, a security weakness in one could have an impact on the others. An iPhone that Apple has designated as an SRD is provided on a renewable, annual basis for security research purposes only and should be utilized in a controlled environment, according to Apple. It also remains Apple’s property.
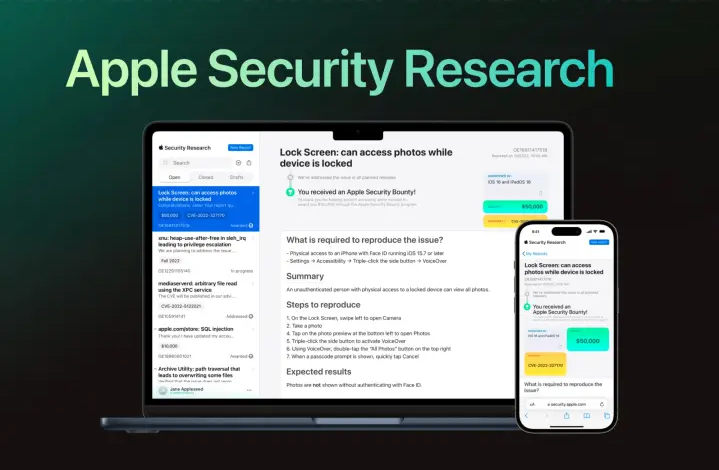
Together with the SRD, Apple makes it simpler to report any vulnerabilities discovered in macOS, packaged programmed, and other Apple operating systems, which gives security researchers an additional incentive. According to Apple, its engineers will examine each submission, conduct investigations, and post notices to acknowledge defects and inform you of your eligibility for the company’s Security Bounty programmed.
Although Apple’s bug bounty programmed offers millions of dollars in rewards, some security experts and developers have found it to be a difficult endeavor. With the debut of the new Apple Security Research website, maybe that will alter.









